Want help to write your Essay or Assignments? Click here
Introduction to Networks (Client/Server, Peer-to-Peer, and Home/Small Office)
Summary Description of the Website’s Structure
The professional support website named Network Computing.com that was retrieved in November 7 is basically built upon a structural theme that informs and reinforces the users mental models on how they can get access to the contents provided. These elements therefore govern the manner in which the navigational systems of the web site mold its user’s mental models on the manner in which information is organized (Kini, 2002).
This therefore points out to the essentials that are required in the development of a site which includes hierarchies and sequences as depicted in the website. The information in the website is organized in a sequential manner an element that is chronologically done with topics aligned in series from the general to the specific subjects. Since this website can be considered as an educational site, there is an incorporation of straight sequences.
Discussion on What I Have Learnt From This Website
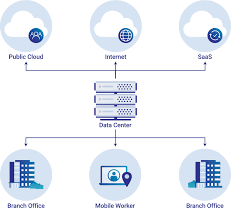
It is essential to point out that one of the subjects that interest me in the website is that which is related to the manner in which Cloud systems are used to cure M&A IT integration challenges. As determined through the website, the integration of IT systems and the transfer of data remains a challenging task. However, companies have the opportunity and the capacity to incorporate the use of cloud systems in the integration of their functions with the aim of streamlining there functions (Kini, 2002).
According to the site, it has been established that data transfer systems and the way in which they are integrated remains an afterthought in M&A negotiations. However, this may represent one of the biggest challenges through the divestment process.
Introduction to Networks
Want help to write your Essay or Assignments? Click here
Some other lines of business owners have faced challenges in the making of more complex systems. Through the use of IT, these business lines have the capacity to strictly timeline there systems through the combination of the cloud systems, a factor that impacts the functions of their organizations (Stephanie, 2016). Large data transfers, data centre approaches to consolidation and the application of level standardization approaches have been also found to be a challenging task for entities, and still becomes more complex across multiple organizations.
The site therefore depicts the answer to the challenges that have been faced in the integration of M&A systems that come from different unexpected sources. Through the utilization of public cloud, organizations are bound to find relief in the issues and the challenges that have been faced in their IT experiences (Stephanie, 2016).
This therefore requires that a divesting approach to a company’s functions is moved to the cloud which creates a neutralizing environment that clarifies data ownership and provides clear projections across the accessed controls.
An instance is given of the Hess Corporation which shares details of the manner in which divestment in the retail and energy marketing industry can be leveraged through the use of other web services such as Amazon. This approach treats the marketing business of an organization as an element that needs to be incorporated in a neutral zone during the process of transition (Stephanie, 2016). Hess Corporation in this case made use of the automation approach in building several servers a day that made use of the AWS tools in the creation of backup systems that would monitor and set up networks.
Introduction to Networks
Want help to write your Essay or Assignments? Click here
Companies that look for opportunities to acquire divested systems may therefore incorporate the proponents of cloud services in its operations and ensure its staff is acquainted with the cloud skills in a move to make the organization appealing to the buyers. This therefore points out organizations in the use and integration of public cloud services as an option to the challenges that have been faced in the IT world (Stephanie, 2016).
However, there are some other factors that need to be considered such as the strategic alignment approaches, financial synergies and the cultural fit, an approach that clearly depicts the need to incorporate infrastructural systems that enable the smooth transition of these systems in the right approach. Some of the helpful links that have broadened my knowledge on this subject therefore include: http://www.cloudsystems.com/
In my view, I find this information essential as my professional resource since it provides insights into several elements that enhance my knowledge on the approaches of integrating the cloud systems to the functions of an organization. With this information, I am in a capacity to decisively adopt the cloud systems within the functions of an entity in as a means of making the functions of such an organization appealing to the clients (Rimac, Borst, & Walid, 2008).
I therefore find this information very essential to many organizations that are struggling to make a transition into the IT world to develop infrastructures that fit into the current culture.
Introduction to Networks
Want help to write your Essay or Assignments? Click here
Evaluation of the Program
The website known as Network Computing.com is an educational site that moulds and informs the minds of its users on several elements as noted in the site. The site provides to its users more informative information on the use of different IT systems in the enhancement of their business functions (Loo, 2003).
The manner in which the site is developed therefore makes it appealing to the users to find the right information required. The information in the website is organized in a sequential manner an element that is chronologically done with topics aligned in series from the general to the specific subjects.
References
Kini, R. B. (2002). Peer-To-Peer Technology: A Technology Reborn. Information Systems Management,19(3), 74.
Loo, A. W. (2003). The Future of Peer-To-Peer Computing. Communications of the ACM, 46(9), 57-61.
Rimac, I., Borst, S., & Walid, A. (2008). Peer-assisted content distribution networks: performance gains and server capacity savings. Bell Labs Technical Journal (John Wiley & Sons, Inc.), 13(3), 59-69. doi:10.1002/bltj.20323
Stephanie Tayengco (2016). The Cloud Cures M&A IT Integration Headaches. Retrived From: http://www.networkcomputing.com/cloud-infrastructure/cloud-cures-ma-it-integration-headaches/2097909404
Introduction to Networks
Want help to write your Essay or Assignments? Click here