A couple of Information technology experts would consent that cloud computing is the most convenient and most dynamic model of message delivery since the birth of internet. Cloud computing has been used by corporate managers and decision makers to help them achieve several financial advantages and protect them from any security threats that could result to tainting of their reputable image and even the longevity of the business itself (Pereira, 2014). In itself, cloud computing is cost-effective and an efficient option to purchasing and sustaining hardware and software in-house. This has been the case since the introduction of Amazon’s S3 (Simple Storage Services) and EC2 (Elastic Compute cloud).
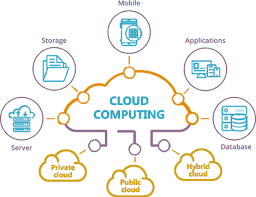
Cloud computing has had various definitions, having different service providers and the available standard organizations giving different definitions of the same. For instance, the National Institute of standards and Technology (NIST) defines cloud computing as “a model for that enables the ubiquitous, convenient, on-demand network access to a pool of shared configurable computing services that can be speedily provisioned and released with minimal management effort. What cloud computing does, is to avail platforms, software, and infrastructure in form of web services using the internet. However the consumers do not know the specific physical location where these services are provided from. They therefore purchase the software and hardware as services rather than physical assets (Pereira, 2014).
Cloud computing is categorized into various classifications. Software, platform, and infrastructure as a service.
Software as a service moves the separation to the highest level in the stack. Most of cloud services such as web-based email and word processing which are offered for free are in this category (Pereira, 2014). It is beneficial for the users since they do not incur any costs of maintenance.
Platform as a service boosts the separation slightly higher and is a surrounding where the already developed and deployed applications are made available by cloud providers. The consumers take advantage of the platforms provided such as Java programming language and oracle databases (Pereira, 2014).
Infrastructure as a service is the minimum class of separation between what consumers desire and the services that are readily available for them to use (Pereira, 2014). Consumers are supplied with raw computing, storage services and networking, this assists them to establish applications and custom services. The cloud provider is in charge of all the physical resources, while the consumer monitors all the other factors mentioned including development tools and operating system (Pereira, 2014).
Technology alongside its tremendous benefits is also faced with security threats. The prevalent threats include cybercrimes. There has been however measures that have been put in place to try and alleviate this challenges (Pereira, 2014). Cloud itself can be used as a means of securing data and also disseminate information among others.
According to (Pereira, 2014) customers ought to get cloud services from the internet. Reports according to (Pereira, 2014) claims that ethics that regulate internet usage and accessibility are used to help clients access the cloud. Through a communication process clients are able to access information and software in the cloud. Correspondence through the cloud is grouped into; outside correspondence, which happens between the cloud and the clients and inner correspondence, which happens inside the cloud’s framework.
Outer correspondence has likenesses with other Internet types of correspondence. Subsequently, according to (Pereira, 2014) the issues experienced by the cloud as a consequence of its Internet highlight are like those of ordinary information and communication technology. These are concerns such as incorporate man-in-the-center, refusal of administration, IP-parodying based flooding, double dealing and listening to private conversations without consent (Pereira, 2014).
Security Challenges
The general problem is that breaches in security are evident in cloud computing (Jansen, 2011). The specific problem is the increasing costs in the prevention and alleviation of breaches in cloud security. Despite the increased growth in the computing technology, a great danger of losing data due to cybercrimes and other related threats exists. Efforts have been made to curb the problem of security issues (Younis, 2013).
One of these measures includes the use of cloud as a tool to secure data and share information among others. Moreover, the insecurity of cloud computing has recently upsurged (Han, 2013). The paper looks into security vulnerabilities in cloud computing and recent solutions posted by different scholars are discussed.
The cloud’s security risks may vary from those of the infrastructure of traditional IT either in intensity, nature, or even both. Several works have been put in place to monitor the cloud’s security challenges from the service model perspective. The identified challenges are classified according to the following domains; communication issues, contractual and legal issues.
Communication Level Challenges
Normally, the services of the cloud are accessed by customers through the Internet (Younis, 2013). Subashini (2011) reports that standard Internet protocols and mechanisms aid in facilitating the communication between the cloud and customers. The process of communication leads to conveyance of either applications or information/data between the cloud and the customers. Virtual Machines (VMs) of the cloud are also in constant communication with each other. Communication through the cloud is classified into; external communication, which occurs between the cloud and the customers and internal communication, which takes place within the cloud’s infrastructure.
External communication has similarities with other Internet forms of communication. Consequently, the problems encountered by the cloud as a result of its Internet feature are similar to those of conventional IT communication (Rong, 2013). These issues include man-in-the-middle, denial-of-service, IP-spoofing based flooding, eavesdropping, and deception (Jansen, 2011).
Contractual and Legal Level Challenges
According to Rong (2013), implementation of cloud computing requires applications and data to be migrated by institutions to the administrative control of Cloud Service Providers (CSP). As a result, several issues crop up such as geographic jurisdictions, performance assurance, compliance with regulatory laws, contract enforcement monitoring etc. These issues are associated with the legalities, physical locations of the data, and service level agreement (SLA).
Cloud computing is an involving term that (Pereira, 2014) defines a cloud computing as an inclusion of software and system software in the datacenterthat satisfies these services. Some of the exceptional features of cloud computing include the illusion of different hardware resources and the ability to pay for the required resources. In a unique way, (Han, 2013) states that some of the features of cloud computing include use of a wide network access, large resource pool, dynamic elasticity, on-demand self-service, and also the some of the metered services that are similar to utility.
In general, cloud computing uses three main service models (Mell, 2011). The first service is software as a service (SaaS), which is software, distributed based representation in which applications are hosted by a service/vendor provider. The models are accessed by customers or the end users via the network, usually the internet. This model some scholars like (Sebesta, 2012) states that it is associated with the pass-as-you-go subscription licensing model. The second computing model is a platform as a service (PaaS) that allows customers to manage the hosting environment (Chen, 2012, March). The third model is the infrastructure as a service (IaaS).
In this model, the customers control everything apart from the datacenter infrastructure (Sebesta, 2012).
Conclusion
Cloud computing is an emergent phenomenon which is set to revolutionize the use of the internet. Nevertheless caution is a needed about it. Moreover, these new technology has made human lives easier, but people need to be careful in understanding the security risks and challenges involved when using these technologies. In this research paper, the core focus of highlighting the challenges, insecurity issues that arise as a result of cloud computing. In summary, the cloud computing has the capacity of becoming a pioneer in the promotion of a safe, virtual and economical solution in the future.
References
Amazon. (2012, April). Amazon web services blog: Amazon S3 – 905 billion objects and
650,000 requests/second. Retrieved from http://aws.typepad.com/aws/2012/04/amazon-s3-905-billion-objects-and-650000-requestssecond.html
Chen, D., & Zhao, H. (2012). Data security and privacy protection issues in cloud computing.In Computer Science and Electronics Engineering (ICCSEE), 2012 International Conference on (Vol. 1, pp. 647-651).IEEE.
Chen, Y., Paxson, V., & Katz, R. H. (2010). What’s new about cloud computing security.University of California, Berkeley Report No. UCB/EECS-2010-5 January, 20(2010), 2010-5.
Chen, Y., Paxson, V., & Katz, R. H. (2010). What’s new about cloud computing security.University of California, Berkeley Report No. UCB/EECS-2010-5 January, 20(2010), 2010-5.
Dikaiakos, M. D., Katsaros, D., Mehra, P., Pallis, G., & Vakali, A. (2009).Cloud Computing: Distributed InternetComputing for IT and ScientificResearch.Internet Computing, IEEE, 13(5), 10-13.
Han, Y. (2013). On the clouds: A new way of computing.Information Technology and Libraries, 29(2), 87-92.
Jansen, W. (2011, January). Cloud hooks Security and privacy issues in cloud computing. In System Sciences (HICSS), 2011 44th Hawaii International Conference on (pp. 1-10).IEEE.
Kuo, A. M. H. (2011). Opportunities and challenges of cloud computing to improve health care services.Journal of medical Internet research, 13(3).
Mell, P., &Grance, T. (2011). The NIST definition of cloud computing.
Pereira, A., Machado, R. J., Fernandes, J. E., Teixeira, J., Santos, N., & Lima, A. (2014).Using the NIST reference model for refining logical architectures. In Computational Science and Its Applications–ICCSA 2014 (pp. 185-199). Springer International Publishing.
Ren, K., Wang, C., & Wang, Q. (2012). Security challenges for the public cloud. IEEE Internet Computing, (1), 69-73.
Rong, C., Nguyen, S. T., & Jaatun, M. G. (2013). Beyond lightning: A survey on security challenges in cloud computing. Computers & Electrical Engineering, 39(1), 47-54.
Ryan, M. D. (2013). Cloud computing security: The scientific challenge, and a survey of solutions.Journal of Systems and Software, 86(9), 2263-2268.
Sebesta, D. J., Schmidt, S., Westerinen, W. J., & Carpenter, T. (2012). U.S. Patent No. 8,161,532. Washington, DC: U.S. Patent and Trademark Office.
SO, K. (2011). Cloud computing security issues and challenges. International Journal of Computer Networks, 3(5).
Younis, M. Y. A., &Kifayat, K. (2013).Secure cloud computing for critical infrastructure: A survey.Liverpool John Moores University, United Kingdom, Tech. Rep.
Want help to write your Essay or Assignments? Click here